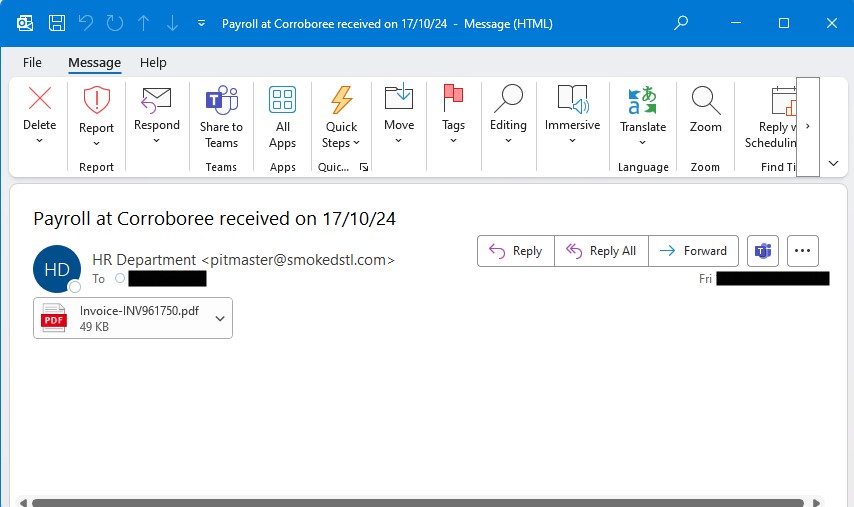
Look out for the email sender. The name ‘HR Department’ is just a made up name. The actual sender in this case, pitmaster@… is likely unknown to you, in fact they have likely been scammed themselves.
The subject is often deliberately enticing. But does it line up with your payroll system, or superannuation fund.
The email body is totally blank. There is no text at all. Take this as being highly suspicious. Keeping this blank is a deliberate method to avoid email filtering scam detection.
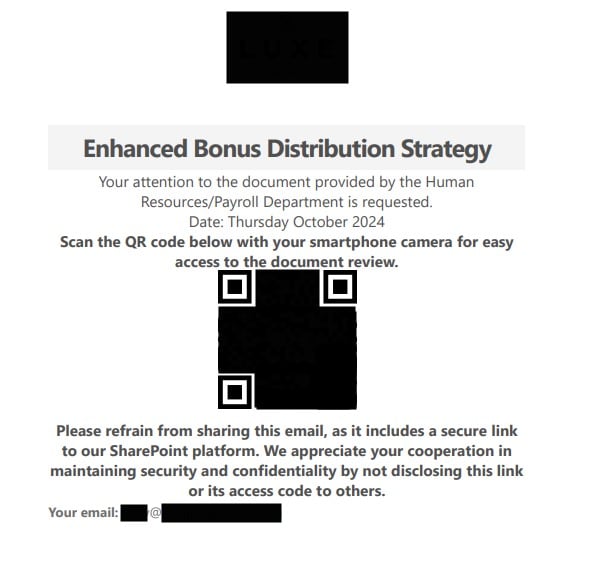
Finally, there is a PDF attachment. Unfortunately, only advanced email filtering software will be able to detect anything unusual in this email, such as the fact that the PDF has a QR code linked to a risky or fraudulent website.